Hackers Send Physical Phishing Letters Impersonating Trezor and Ledger
Cybersecurity experts warn of a mail-based phishing scam urging users to comply with fake authentication checks, threatening wallet access if ignored.
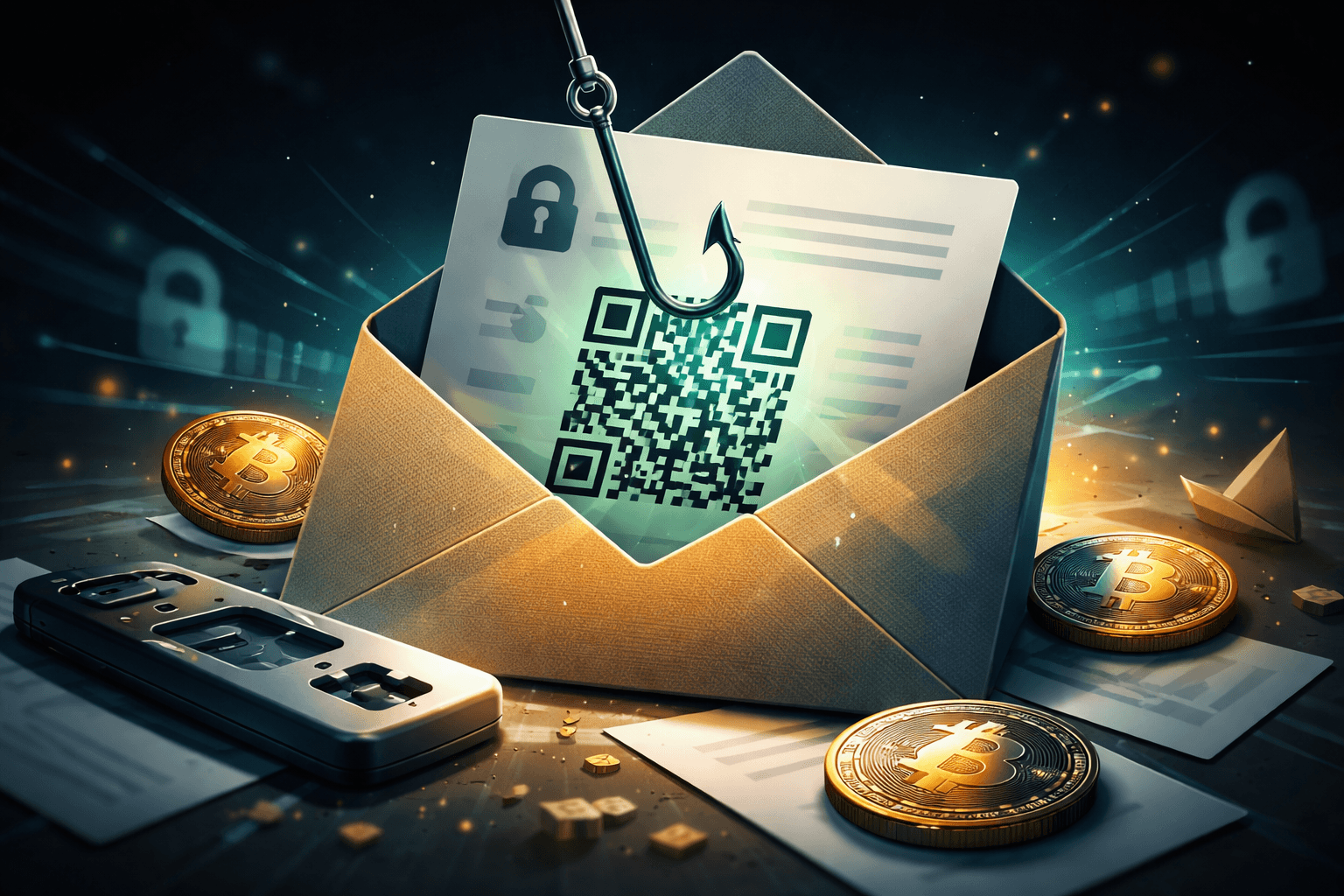
Trezor and Ledger hardware wallet users are facing a phishing scam delivered through physical mail, according to cybersecurity experts. The fraudulent letters impersonate official notices and demand a mandatory authentication check before February 15, 2026, warning that access to the device will be revoked if ignored. These letters direct recipients to malicious sites designed to harvest seed phrases, enabling attackers to seize cryptocurrency assets. This incident highlights an ongoing shift in phishing tactics toward physical delivery channels to exploit trust in official-looking correspondence.
- Seed Phrase: A sequence of words generated by a cryptocurrency wallet, serving as the master key for restoring the wallet and accessing its funds.
- Hardware Wallet: A physical device, such as those made by Trezor or Ledger, that stores private keys offline to protect against online hacking attempts.
- Phishing: A fraudulent attempt to obtain sensitive information by disguising as a trustworthy entity, often through deceptive communication channels.